Chapter 5: Selection & Interfaces
Core product introduction, typical wiring, interface logic, and comprehensive product feature comparison
Selecting the right products for a cybersecurity monitoring system requires understanding both the functional capabilities of each component and the interface requirements for integration. This chapter introduces the five core product categories that form the foundation of a complete monitoring architecture, presents the interface and connection logic that defines how these products communicate, and provides a detailed feature comparison table to guide procurement decisions.
5.1 Core Product Introduction
The five core product categories — SIEM Platform, Network TAP/Bypass, Log Collector Appliance, Threat Intelligence Platform, and SOAR Automation Platform — work together to provide complete monitoring coverage from data collection through automated response. Each product category has distinct technical requirements and selection criteria that must be evaluated against the specific deployment scenario.

Figure 5.1: Core Cybersecurity Monitoring Product Lineup — Enterprise SIEM Platform, Network TAP/Bypass Appliance, Log Collector, Threat Intelligence Platform, and SOAR Automation Platform in professional product showcase.
| Product Category | Primary Function | Form Factor | Key Specification | Typical Deployment |
|---|---|---|---|---|
| Enterprise SIEM Platform | Event correlation, alerting, investigation | 2U/4U rack server or VM | 50,000+ EPS, 1 PB+ storage | Central data center |
| Network TAP/Bypass | Passive traffic capture without disruption | 1U rack appliance | 10/40/100G, failopen mode | Core network inline |
| Log Collector Appliance | Multi-protocol log aggregation and normalization | 1U rack appliance or VM | 20,000 EPS per collector | Distributed (per site) |
| Threat Intelligence Platform | IOC management, threat feed aggregation | 2U rack server or VM | 100M+ IOC capacity | Central or cloud |
| SOAR Automation Platform | Playbook automation, incident orchestration | VM or SaaS | 1,000+ pre-built playbooks | Central SOC |
5.2 Typical Wiring & Interface Logic
The interface and connection logic defines the exact protocols, ports, and data flows between all components in the monitoring architecture. Understanding this interface map is essential for network firewall rule configuration, capacity planning, and troubleshooting. The diagram below shows the complete interface topology from data sources through the log collector to the SIEM platform and its downstream integrations.
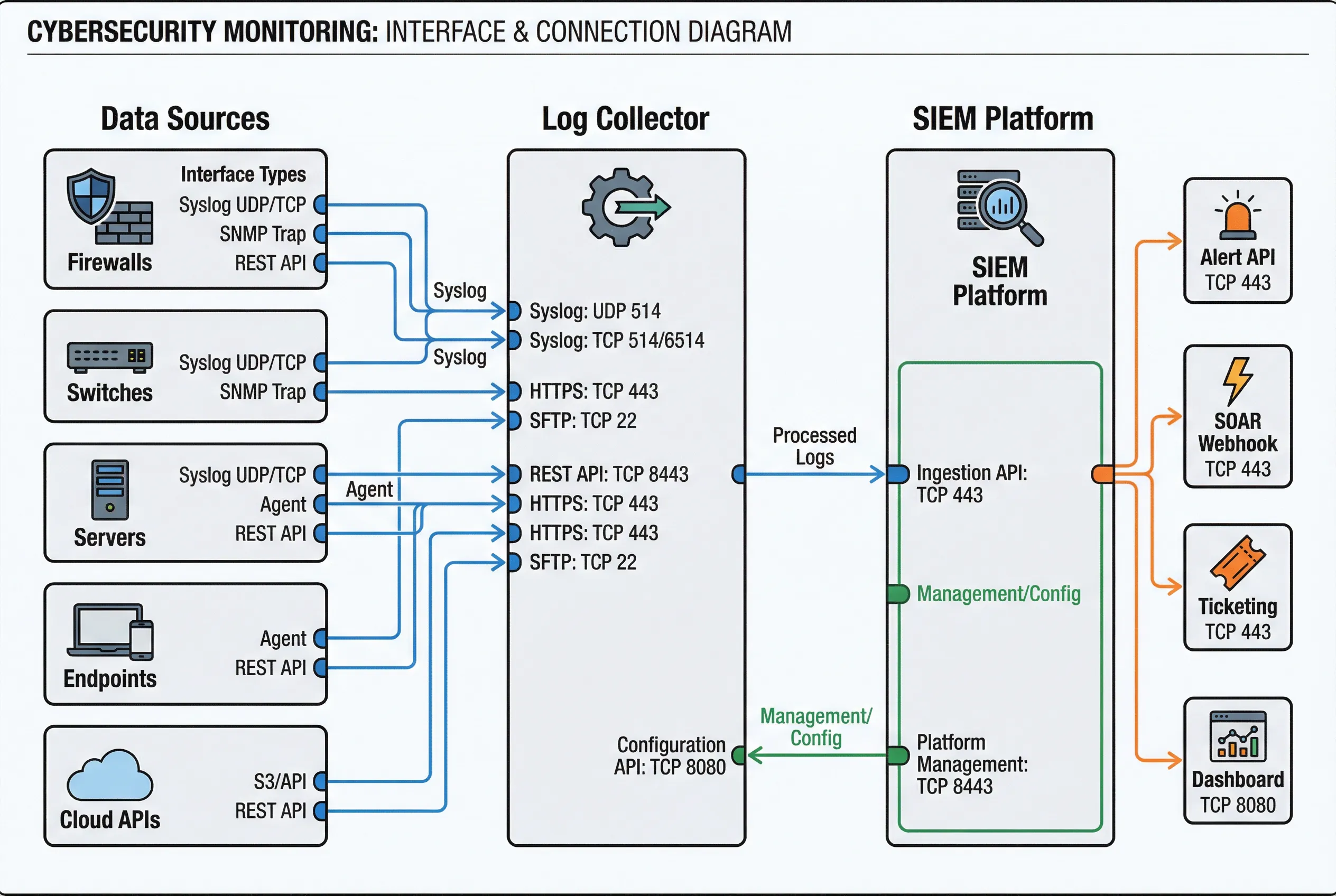
Figure 5.2: Interface and Connection Logic Diagram — Data source interfaces (left), Log Collector port specifications (center), SIEM Platform output interfaces (right), with color-coded connections: blue for log ingestion, orange for alerts, green for management.
| Interface | Protocol | Port | Direction | Encryption | Notes |
|---|---|---|---|---|---|
| Syslog (UDP) | Syslog RFC 3164/5424 | UDP 514 | Source → Collector | None (plain) | Legacy devices; use TCP for reliability |
| Syslog (TCP/TLS) | Syslog over TLS | TCP 6514 | Source → Collector | TLS 1.2+ | Recommended for all new deployments |
| HTTPS API | REST/JSON over HTTPS | TCP 443 | Source → Collector | TLS 1.2+ | Cloud services, modern applications |
| SFTP | SSH File Transfer Protocol | TCP 22 | Source → Collector | SSH | Batch log file transfer |
| Log Forwarding | Proprietary/REST | TCP 8443 | Collector → SIEM | TLS 1.2+ | Normalized events from collector to SIEM |
| Alert API | REST/JSON over HTTPS | TCP 443 | SIEM → SOAR | TLS 1.2+ | Alert forwarding to SOAR for automation |
| Ticketing | REST/JSON over HTTPS | TCP 443 | SIEM → ITSM | TLS 1.2+ | Incident ticket creation in ServiceNow/Jira |
| Dashboard | HTTPS | TCP 8080/443 | Browser → SIEM | TLS 1.2+ | Analyst workstation access |
5.3 Core Product Feature Comparison Table
The following comprehensive feature table enables direct comparison of the five core product categories across all critical functional dimensions. This table serves as the primary reference for procurement evaluation and gap analysis when assessing existing tooling against the reference architecture requirements.
| Feature Category | Feature | SIEM Platform | Network TAP | Log Collector | Threat Intel | SOAR Platform |
|---|---|---|---|---|---|---|
| Data Collection | Syslog (UDP/TCP/TLS) | ✓ Primary | — | ✓ Primary | — | — |
| REST API Integration | ✓ | — | ✓ | ✓ | ✓ | |
| Network Packet Capture | Optional | ✓ Primary | — | — | — | |
| Agent-based Collection | ✓ | — | ✓ | — | — | |
| Processing | Log Parsing & Normalization | ✓ | — | ✓ Primary | — | — |
| Real-time Correlation | ✓ Primary | — | — | — | — | |
| ML Anomaly Detection | ✓ | — | — | — | — | |
| IOC Enrichment | ✓ | — | Basic | ✓ Primary | ✓ | |
| Response | Alert Generation | ✓ Primary | — | — | ✓ | ✓ |
| Automated Playbooks | Basic | — | — | — | ✓ Primary | |
| Ticketing Integration | ✓ | — | — | — | ✓ Primary | |
| Firewall Block Action | Via SOAR | — | — | — | ✓ Primary | |
| Compliance | Audit Log Retention | ✓ Primary | — | Buffer | — | — |
| Compliance Reporting | ✓ Primary | — | — | — | Partial | |
| Chain of Custody | ✓ | — | — | — | — | |
| Operations | High Availability | ✓ Cluster | ✓ Failopen | ✓ Active-Active | ✓ HA Pair | ✓ HA |
| Multi-tenancy | ✓ | — | Partial | — | ✓ | |
| API Management | ✓ | — | ✓ | ✓ | ✓ Primary |
Legend: ✓ = Full support (primary function); Partial = Limited or optional support; — = Not applicable